How We Work
Our Unique Ongoing 4-Step Process
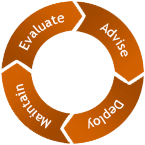 When choosing Entec as a technology partner, your company will benefit from a continuous 4-step process we’ve developed over years of solving customer challenges.
When choosing Entec as a technology partner, your company will benefit from a continuous 4-step process we’ve developed over years of solving customer challenges.
Evaluate - Advise - Deploy - Maintain & Protect
The Process
1Evaluate:
Entec will study and learn your business and processes and then apply the technology that supports them.
2Advise:
After examining the four key areas of security, availability, redundancy and cost, we’ll recommend a technology plan that fits your business needs.
3 Deploy:
Next our engineers step in and build the system you need designed within your budget.
4 Maintain & Protect:
Once your solution has been deployed, we monitor everything, provide proactive system maintenance, and make sure you’re secure and protected, too.
You guys are hands down the best and most responsive IT team at any business I work with, no kidding, and I work with a great deal of businesses of all kinds. Thanks!! It makes our life easier!!
Solving Problems — even ones you didn’t know you had.
From security issues and out-dated hardware to inefficiencies that frustrate your people in their work, every system has “hidden” issues and headaches. We find them. And instead of patchwork fixes, we uncover how they got there to begin with and make sure they don’t show up again.
Once you’re optimized, we’ll keep you ahead of change.
And remember, our 4-step process is ongoing. With technology moving so fast, we’re continually re-evaluating where you stand. We can advise you on where you need to go next and provide the support you need to get there.
WORK WITH ENTECFeatured Services
Entec offers a wide range of services and customized options based on the individual needs of our clients. Here are some of our most utilized packages.
